Building a secure payment system is one of the most technically demanding and highest-stakes challenges in web application development. Payment processing sits at the intersection of complex API integration, strict security requirements, legal compliance obligations, and zero-tolerance reliability expectations. A bug in a payment system does not just cause a bad user experience — it can result in financial loss, regulatory penalties, legal liability, and permanent reputational damage that destroys customer trust.
This guide provides a comprehensive technical walkthrough of building a secure payment system using custom APIs in 2026. Whether you are building an e-commerce platform, a subscription SaaS product, a marketplace with split payments, or a custom billing system, the principles and practices covered here will help you build payment infrastructure that is secure, compliant, and reliable.
Understanding PCI DSS: The Payment Security Standard You Cannot Ignore
The Payment Card Industry Data Security Standard, or PCI DSS, is a set of security requirements that any organisation that accepts, processes, transmits, or stores payment card data must comply with. PCI DSS is maintained by the PCI Security Standards Council, founded by American Express, Discover, JCB International, Mastercard, and Visa. Non-compliance can result in fines from card networks, loss of the ability to accept card payments, mandatory forensic investigations after breaches, and liability for fraudulent charges.
PCI DSS version 4.0, the current standard, organises requirements into twelve domains covering network security, cardholder data protection, vulnerability management, access control, monitoring, and policy. The specific requirements that apply to your payment system depend on how you handle card data.
The most important principle for building a secure payment system with custom APIs is minimising your PCI DSS scope through payment tokenisation. If raw card data never touches your servers — your customers' card numbers go directly to a compliant payment processor like Stripe, and your system receives only a token that represents the card — your PCI DSS compliance scope drops dramatically to SAQ A or SAQ A-EP depending on your integration method, rather than the much more extensive SAQ D that applies to systems that process raw card data.
Payment Tokenisation: Keeping Card Data Off Your Servers
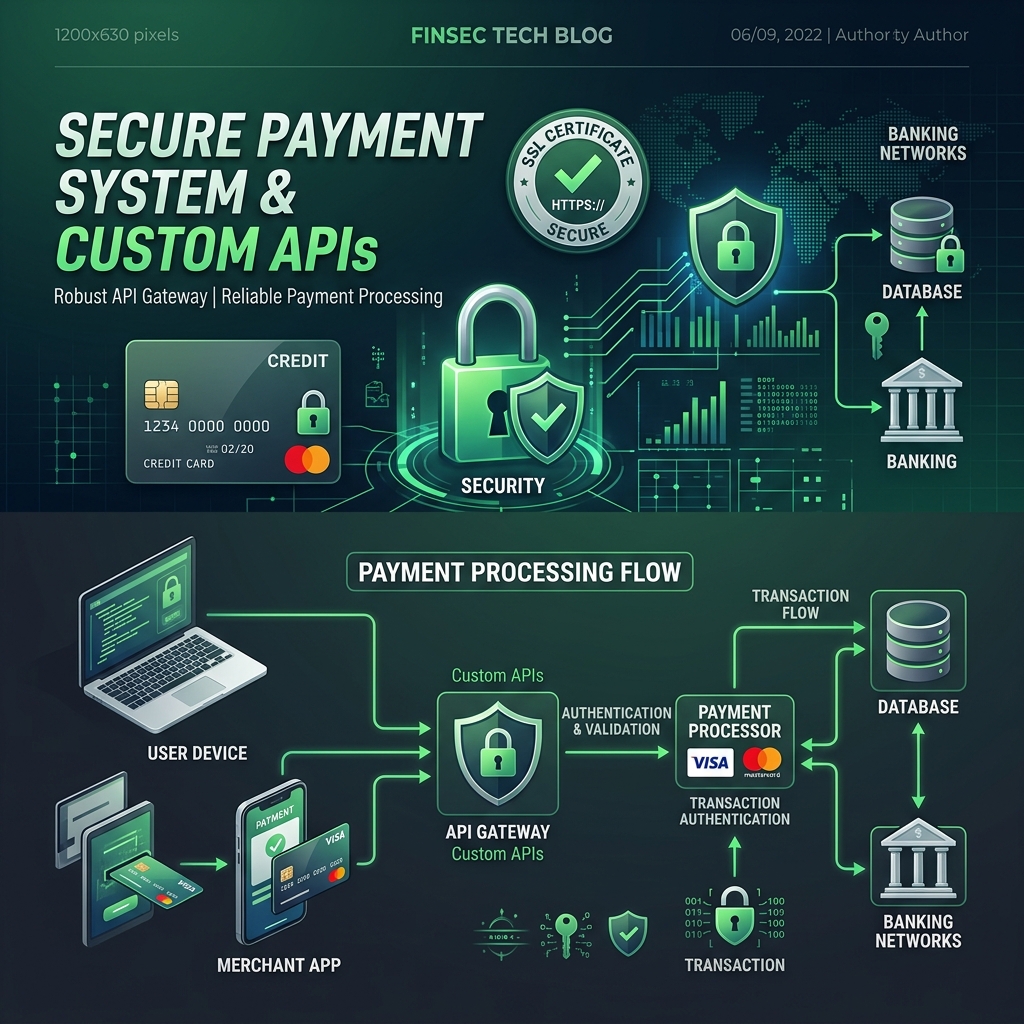
Payment tokenisation is the foundational security architecture decision for any secure payment system. Rather than collecting card numbers on your web form and transmitting them to your backend, you implement a tokenisation flow where the sensitive card data goes directly from the customer's browser to the payment processor's servers, and only non-sensitive tokens are shared with your application.
Stripe's implementation of this is Stripe.js and Stripe Elements, a set of pre-built UI components that render card input fields hosted on Stripe's domains within iframes on your payment form. When the customer enters their card number, it is transmitted directly to Stripe's servers over encrypted connections. Stripe validates the card data, stores it securely in their PCI-certified systems, and returns a PaymentMethod or SetupIntent token to your frontend JavaScript. Your frontend sends this token to your backend, which then calls Stripe's API to create a payment intent using the token. At no point does raw card data touch your servers.
This tokenisation approach is the correct architecture for secure web payment systems in 2026. Any alternative that involves routing raw card numbers through your backend dramatically increases your PCI DSS scope, liability, and the catastrophic consequences of a security breach.
Stripe API Integration: A Secure Payment System Architecture
Stripe is the most developer-friendly and technically sophisticated payment processor available, and building a secure payment system on Stripe's APIs provides access to an extraordinarily comprehensive set of payment capabilities backed by Stripe's PCI-compliant infrastructure. Understanding the right architectural patterns for Stripe API integration prevents the security mistakes that frequently appear in production payment systems.
Payment Intents: The Modern Stripe Payment Flow
The Payment Intents API is the correct approach for one-time payments in modern Stripe integrations. The flow begins when your customer initiates checkout and your backend creates a Payment Intent by calling the Stripe API with the payment amount, currency, and customer information. Stripe returns a Payment Intent object with a client key that your backend passes to your frontend. Your frontend uses this client key with Stripe.js to confirm the payment, handling Strong Customer Authentication challenges like 3D Secure automatically. When the payment is confirmed, Stripe sends a webhook to your backend to update the order status.
The Payment Intents API handles Strong Customer Authentication automatically, which is a legal requirement in Europe under PSD2 and is increasingly common elsewhere. Without Payment Intents, European payments will fail authentication challenges, resulting in declined transactions that directly impact revenue from European customers.
Idempotency: Protecting Against Duplicate Charges
One of the most critical security and reliability controls in a payment API system is idempotency. Network requests sometimes fail or time out without a clear response, leaving your application uncertain whether the payment was processed. Without idempotency, retrying a failed payment request might result in double charging the customer, which is both a terrible user experience and potentially illegal in some jurisdictions.
Stripe's API supports idempotency keys, unique strings that you generate and include with every payment API request. If a request fails and you retry it with the same idempotency key, Stripe will not process the payment again — it will return the result of the original request. Generate idempotency keys deterministically from your internal order or transaction ID so the same key is used if you retry after a timeout. Store idempotency keys in your database alongside the order, and never retry a payment without including the original idempotency key.
Webhook Security: Verifying Payment Events Are Legitimate
Webhook security is an aspect of payment system security that developers frequently implement incorrectly, creating a critical vulnerability where attackers can send fake payment success events to your webhook endpoint, tricking your system into believing payments have been completed when they have not.
Stripe signs every webhook event with a signature derived from your webhook secret and the event payload. Your webhook handler must verify this signature before processing any event. Stripe provides libraries for every major programming language that handle signature verification with a single function call.
In Laravel, webhook verification with Stripe should be implemented using the raw request body rather than the parsed JSON, because PHP's request parsing can alter the body in ways that invalidate the signature. Read the raw input directly from the request body, compute the expected signature using your webhook secret, and compare it with the signature in the Stripe-Signature header using a timing-safe string comparison function to prevent timing attacks. Only proceed to process the event after signature verification passes.
Additional webhook security practices include storing incoming webhook payloads in a database before processing them, implementing idempotency for webhook handling so duplicate deliveries do not cause duplicate state changes, processing webhooks asynchronously via a queue rather than synchronously in the request handler, and implementing webhook delivery monitoring to alert when expected events are not received within expected timeframes.
Fraud Prevention in Custom Payment Systems
Payment fraud is a persistent and expensive threat for any business accepting online payments. Card testing attacks, where fraudsters use automated scripts to test stolen card numbers against your payment system in bulk, can result in significant Stripe fees, card network disputes, and potential penalties if your fraud rate exceeds thresholds. Carding attacks that result in successful fraudulent charges create chargeback costs and chargeback ratio penalties.
Stripe Radar is Stripe's machine learning-powered fraud prevention system that evaluates every payment for fraud risk using signals including card fingerprint, device fingerprint, IP address, billing address verification, velocity patterns, and pattern matching against known fraud indicators. Stripe Radar provides a base level of fraud prevention automatically, and Stripe Radar for Fraud Teams adds rule customisation that allows you to implement business-specific fraud rules.
Beyond Stripe Radar, implement application-level fraud controls: rate limiting on your payment initiation endpoints to prevent automated card testing, CAPTCHA on checkout forms that show anomalous patterns, velocity checks that flag or block accounts making payments from multiple cards within short time windows, address verification system checks that compare billing addresses against card issuer records, and CVV verification requirements for all card-present-absent transactions.
Building Refund and Dispute Management APIs
A complete secure payment system includes comprehensive refund and dispute, or chargeback, management capabilities. Refunds must be processed correctly against the original payment to maintain proper accounting, and dispute responses require retrieving evidence from your system quickly.
Implement a refund API that validates refund eligibility before calling Stripe's Refund API. Eligibility checks should include confirming the payment is in a capturable or captured state, confirming the refund amount does not exceed the original payment amount minus previous refunds, confirming the payment is within the refundable window, and confirming the requesting user is authorised to issue refunds for that payment.
Store refund events from Stripe webhooks alongside your payment records. Update your order and financial records atomically with the refund record creation so your accounting is always consistent with Stripe's records. Implement reconciliation processes that periodically compare your payment database with Stripe's payment records to detect discrepancies before they compound.
Subscription and Recurring Payment Architecture
For SaaS products and any business with recurring revenue, secure subscription payment architecture requires additional considerations beyond one-time payments. Subscription payments involve stored payment methods that are charged automatically at future dates, requiring careful attention to payment method updates, failed payment handling, and dunning management.
Implement Stripe's customer portal for self-service subscription management, allowing customers to update their payment methods, view invoice history, upgrade or downgrade plans, and cancel subscriptions without contacting support. This dramatically reduces support costs while improving customer satisfaction.
Build a robust dunning system for failed subscription renewals. When a renewal payment fails, implement a retry schedule that attempts the charge on days one, three, seven, and fourteen after initial failure, with customer notification emails at each stage. Use Stripe's Smart Retries feature which uses Stripe's machine learning to time retry attempts when the probability of success is highest. After the final retry, pause the subscription and provide a grace period for the customer to update their payment method before cancelling.
If you need expert assistance designing and building a secure payment system with custom APIs for your business, I specialise in payment API development for e-commerce, SaaS, and marketplace platforms serving businesses across the US, UK, Canada, Germany, and globally. I have extensive experience with Stripe integrations including complex marketplace and connect implementations.
Contact me today to discuss your payment system requirements and build a secure, compliant payment infrastructure that your customers and your business can depend on.
